So, I was kicked back, having a drink or two and enjoying my time away from vista (more on that in another blog) and thinking. For some reason, my mind went to WWII, and America's invention of a radio jamming defense system. It dawned on me that the same technique could be applied in reverse to protect wireless access points.
Current wireless protection depends on encryption standards. While these standards can be rather good, they rely on the premise that the data will be long out dated and useless by the time an attacker could crack the encryption protecting it. Indeed, (theoretically speaking), a 16 character password using upper case, lowercase, special characters (not on the top row) and numbers would take more than one person's life time to break.
However, as computers and processors become more and more powerful, the time required to break encryption dramatically falls to a mere fraction of what it once was. Current computers would take only a few seconds to crack the encryption that enigma machines used in WW2.
So why bother with a jamming procedure which was invented in WW2? Because it is the basic premise that can be replicated and updated to fit our needs today. The machine that I am talking about worked using a device similar to the old rotating drum inside a piano. The device would cycle channels, and only using another key that matched exactly would allow you to change channels in sync with anyone else you needed to communicate with. By the end of the war, the German's could not listen in on American or British communication, and could not jam a broad enough spectrum of channels to prevent communication either. Here is the basic outline:
You have a large corporate campus. AP's are scattered all over it so that employees can use laptops to complete work. Each laptop is set up with special software that syncs with the AP controllers. Every one second (probably less, 250ms would probably be better) the channel changes on the AP's. The laptops change along with the AP's, so the connection is not lost.
Now, this prevents someone from simply pulling ivs (you did read my wep hacking tut, correct?) But it doesn't prevent them from scanning channels, and eventually discovering the pattern.
So you have to use a jammer as well. This operates at the same rate as the AP's, except it jams every channel except for the one in use. This way, their AP should continue to fail to find any transmissions, and should hopefully be instantly disconnected from any connection they may get on accident.
Just a thought, and requires a lot more in depth though and engineering than this blog entry includes.
Friday, February 29, 2008
Thursday, February 28, 2008
Interim Post
This isn't really a full entry, but I thought it was worth a read. This website has a list of security certifications, their cost, difficulty, standing in the IT world, and some commentary on the content of the exam.
Anyone who is interested in Network Security should have a look at it.
Anyone who is interested in Network Security should have a look at it.
Monday, February 25, 2008
Default Security
So, I was browsing the SANS top 20 security risks of 2007 here and noticed they mentioned the weak or complete lack of default passwords, and/or prompting for new passwords. I also ran into this discussion on the backtrack.org forums.
The essential problem is that manufacturers add setup wizards which either skip the subject of passwords and security, or only touch on the default password. Everyone in networking knows that a linksys router has the user name and password of admin, for example.
So why can't manufacturers:
A) Enable high security features by default (IE WPA)?
B) Randomly generate a 16 character password with upper and lower case letters, and numbers?
c) Ask users if they want to enable low security features, such as wireless communication or auto-form completion?
Don't manufacturers have that responsibility? Now, it is understandable that companies like Cisco do not add any programming to their high end equipment, as only certified professionals are expected to purchase and implement the equipment anyway. But an employee with a poorly configured PDA could pose a huge security risk to the company.
That's not to mention bluetooth devices that still have the default code of 0000.
While it's true that the ultimate responsibility is that of the end user, manufacturers should not be promoting products that are easy to use and "easy to install" if they are not equally easy to secure.
The essential problem is that manufacturers add setup wizards which either skip the subject of passwords and security, or only touch on the default password. Everyone in networking knows that a linksys router has the user name and password of admin, for example.
So why can't manufacturers:
A) Enable high security features by default (IE WPA)?
B) Randomly generate a 16 character password with upper and lower case letters, and numbers?
c) Ask users if they want to enable low security features, such as wireless communication or auto-form completion?
Don't manufacturers have that responsibility? Now, it is understandable that companies like Cisco do not add any programming to their high end equipment, as only certified professionals are expected to purchase and implement the equipment anyway. But an employee with a poorly configured PDA could pose a huge security risk to the company.
That's not to mention bluetooth devices that still have the default code of 0000.
While it's true that the ultimate responsibility is that of the end user, manufacturers should not be promoting products that are easy to use and "easy to install" if they are not equally easy to secure.
Thursday, February 21, 2008
Hex Editing
What is hex editing? Hex editing is a method of altering files based on hex instead of using given editing software, such as notepad or visual basic. This is not the quickest method of altering a file, but it will allow you to access portions of files that are otherwise concealed.
So is this a security concern? Absolutely. hex editing can be used on data in system memory as well as data stored on the hard drive.
Here I'm using FlexHEX. You can see that selecting the hex will also show you the plain text translation, and vice versa.


This is how easy it is to edit the text in a text file. You can also alter checksums as such:

Note that I did not alter a file from an actual program, because it is illegal. Tampering with any files from an installed or running program is considered reverse engineering.
So is this a security concern? Absolutely. hex editing can be used on data in system memory as well as data stored on the hard drive.
Here I'm using FlexHEX. You can see that selecting the hex will also show you the plain text translation, and vice versa.


This is how easy it is to edit the text in a text file. You can also alter checksums as such:

Note that I did not alter a file from an actual program, because it is illegal. Tampering with any files from an installed or running program is considered reverse engineering.
Monday, February 18, 2008
Security Videos
For this blog, I'll just link to some interesting security videos.
Hacking Cisco
Cisco Security Training Video (cheesy)
Understanding IPSEC
Hacking Methodologies
Ethical Hacker
And a video from the SANS institute on Security Certification
Hacking Cisco
Cisco Security Training Video (cheesy)
Understanding IPSEC
Hacking Methodologies
Ethical Hacker
And a video from the SANS institute on Security Certification
Friday, February 15, 2008
making a Bart PE setup disk
Making a Bart PE disk is both more and less difficult than making a nLite disk. It is easier because you can make an image immediately, using no additional parameters. However, to actually make a useful disc, there are substantially more steps involved.
I was going to do a tutorial on this, but I do not have the time. Instead, I will add a few highlights.
Diversity
Bart PE is a live install, which means it installs to RAM, but runs like a fully operational OS. Because it also has full network support, it allows you to install an OS to a computer from a remote location. What is the advantage of this? Well, lets say you have two or more domains that clients must be configured for, and multiple brands of workstations. How will you fit all of that on a single CD, which only has enough space for one OS?
The answer is to put multiple images on a server, and add a file browser to Bart PE. Simply choose the image you wish to install from the server and run with it.
Security
nLite is great for convenience, but if anyone ever steals a CD, your CD key and any pre-installed software is now compromised. Simply stealing a Bart PE is but a single step in several more requirements. First, none of the images are stored on the disk, so you must have a password with permissions to access them. If the thief manages to do this, and install an image, they will still need a viable domain logon. If they change the admin password, they have only been able to get a free copy of XP (through a lot of work) but still don't have access to any data.
While this is far from unbreakable (there are several ways around the security) it is still better than no security at all.
Options
You can preload some diagnostic tools, virus scanners, and other useful third party tools. These can be run from the live install, in the even that the computer won't boot. This can greatly simplify the troubleshooting process, saving hours of work and therefore money.
Future Proofing
Because the image is not on the disk, it can be updated, removed, and new images added without any changes to the Bart PE disc. This is a great boon for administrators that do not want to waste time re-creating restore discs.
Drawbacks
Bart PE is not perfect. It requires knowledge of passwords, domain names, and image types. This means installation takes longer and should only be performed by qualified personnel.
Furthermore, because the images are installed over the network, a server must be dedicated for this purpose and enough bandwidth must be reserved. Smaller companies may find this more difficult, and it further increases the amount of time required for an install.
I did find a tutorial that was already created.
I was going to do a tutorial on this, but I do not have the time. Instead, I will add a few highlights.
Diversity
Bart PE is a live install, which means it installs to RAM, but runs like a fully operational OS. Because it also has full network support, it allows you to install an OS to a computer from a remote location. What is the advantage of this? Well, lets say you have two or more domains that clients must be configured for, and multiple brands of workstations. How will you fit all of that on a single CD, which only has enough space for one OS?
The answer is to put multiple images on a server, and add a file browser to Bart PE. Simply choose the image you wish to install from the server and run with it.
Security
nLite is great for convenience, but if anyone ever steals a CD, your CD key and any pre-installed software is now compromised. Simply stealing a Bart PE is but a single step in several more requirements. First, none of the images are stored on the disk, so you must have a password with permissions to access them. If the thief manages to do this, and install an image, they will still need a viable domain logon. If they change the admin password, they have only been able to get a free copy of XP (through a lot of work) but still don't have access to any data.
While this is far from unbreakable (there are several ways around the security) it is still better than no security at all.
Options
You can preload some diagnostic tools, virus scanners, and other useful third party tools. These can be run from the live install, in the even that the computer won't boot. This can greatly simplify the troubleshooting process, saving hours of work and therefore money.
Future Proofing
Because the image is not on the disk, it can be updated, removed, and new images added without any changes to the Bart PE disc. This is a great boon for administrators that do not want to waste time re-creating restore discs.
Drawbacks
Bart PE is not perfect. It requires knowledge of passwords, domain names, and image types. This means installation takes longer and should only be performed by qualified personnel.
Furthermore, because the images are installed over the network, a server must be dedicated for this purpose and enough bandwidth must be reserved. Smaller companies may find this more difficult, and it further increases the amount of time required for an install.
I did find a tutorial that was already created.
Labels:
backup,
Bart PE,
live install,
Restore,
streamline
Wednesday, February 6, 2008
Honeypots
Honeypots are servers set to run in a DMZ with software and data that appears to be genuine company information. By tricking attackers into believing that this fake information is real, it deters them from further probing on the network. But they do more than just this. Some basic information on honey pots can be found at honeypots.net.
So how much further can you go with honey pots? How cost effective and efficient are they?
This article goes into great detail about defeating honeypots and their purpose. This detail becomes extremely technical, so be warned. I will try to do a break down of it further along.
Honeypots are not just a tool used by independent companies to thwart hackers. A project has been created to categorize and record all malicious activity on honeypots world wide. You can find information on this project at the honeynet website. The SANS website also has an entire paper published that goes into detail about honeypots. This can be found on the SANS website.
Now lets look at the potential of a honeypot, past being a simple false positive for attackers. There are two things than a honeypot can be: proactive and reactive.
Proactive honeypots: These honeypots interact with the attackers, disconnecting and banning them from the network, or returning malicious code to their machines. The later is still illegal, and the distribution of damaging code cannot be suppressed once it is released. If the attacker is on a legitimate network, the entire network could be infected and compromised.
It also has the downside of advertising your security system as soon as the attack is reciprocated, allowing the attacker enough information to attempt to bypass that security function when they attempt a second attack.
Reactive honeypots: Despite the name, these are considered "passive" honeypots. Instead of actively fighting back against attackers, these honeypots gather information on their habits, how they react to certain types of information, even their reaction upon discovering that they are in a honeypot. Though these are mainly used to prevent hackers from penetrating further into the network, they can also be used to track the location of the attacker, and block entire ranges of IP addresses.
Both types of honeypots can also attract spam attacks, absorbing what would otherwise be a very annoying stream of unwanted messages.
So how much further can you go with honey pots? How cost effective and efficient are they?
This article goes into great detail about defeating honeypots and their purpose. This detail becomes extremely technical, so be warned. I will try to do a break down of it further along.
Honeypots are not just a tool used by independent companies to thwart hackers. A project has been created to categorize and record all malicious activity on honeypots world wide. You can find information on this project at the honeynet website. The SANS website also has an entire paper published that goes into detail about honeypots. This can be found on the SANS website.
Now lets look at the potential of a honeypot, past being a simple false positive for attackers. There are two things than a honeypot can be: proactive and reactive.
Proactive honeypots: These honeypots interact with the attackers, disconnecting and banning them from the network, or returning malicious code to their machines. The later is still illegal, and the distribution of damaging code cannot be suppressed once it is released. If the attacker is on a legitimate network, the entire network could be infected and compromised.
It also has the downside of advertising your security system as soon as the attack is reciprocated, allowing the attacker enough information to attempt to bypass that security function when they attempt a second attack.
Reactive honeypots: Despite the name, these are considered "passive" honeypots. Instead of actively fighting back against attackers, these honeypots gather information on their habits, how they react to certain types of information, even their reaction upon discovering that they are in a honeypot. Though these are mainly used to prevent hackers from penetrating further into the network, they can also be used to track the location of the attacker, and block entire ranges of IP addresses.
Both types of honeypots can also attract spam attacks, absorbing what would otherwise be a very annoying stream of unwanted messages.
Hacking WPA
DISCLAIMER: Yes, this will show you how to hack into a wireless network. This is very much ILLEGAL. The purpose of this writeup is for educational purposes only. I am demonstrating the weakness of WPA encryption on my own network. If you wish to try this for yourself, I suggest you buy a wireless router and attempt to crack that.
_____________________________________________________________________
Okay, so I'm not going to back track (forgive the pun) through the previous tutorial. If you aren't certain how to get to where I'm beginning this tutorial at, scroll down and read hacking WEP. It will fill you in on everything except putting your card into monitor mode and such.
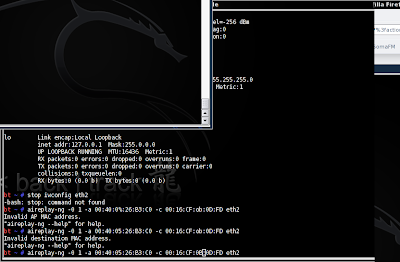
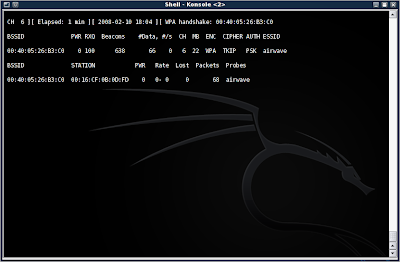
So, first you will need to start up airodump-ng and capture packets from the AP. This time, however, do not add the --ivs, as you will want ALL the data in the packets. Look in the upper right corner of the window, just after the date and time. You will notice that the area is black and empty. This is where the four-way WPA handshake will show up when you have attained it. I will explain that in more detail later.
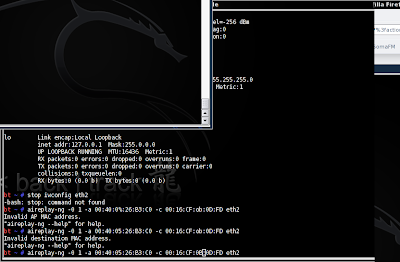
I will assume that you are now collecting packets in monitor mode. Packets by themselves are completely useless for cracking WPA. What we are interested in is the four-way handshake. To get this, we will use aireplay-ng to perform a deauth (de-authentication) attack, disconnecting the client from the AP, and forcing it to reconnect... also giving away the four-way handshake.
To do this, type in aireplay-ng -0 1 -a (AP MAC) -c (Client MAC) (your NIC)
Mine was aireplay-ng -0 1 -a 00:40:05:26:B3:C0 -c 00:16:CF:0B:0D:FD eth2
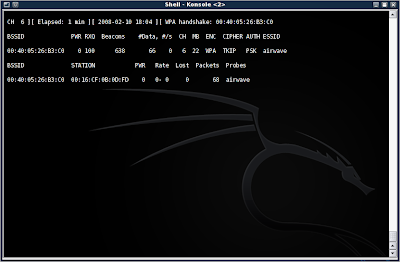
Now you should see a handshake appear in the window containing your running (you did leave it running, right?) airodump-ng program:
Now we need to get the key. Just as in the WEP cracking tutorial, I am going to make you do some of your own leg work. You will need to find a dictionary word list. You can also make your own, and add the pass phrase to the list. This screenshot shows an example of the list I made in a few seconds to show you the next steps:
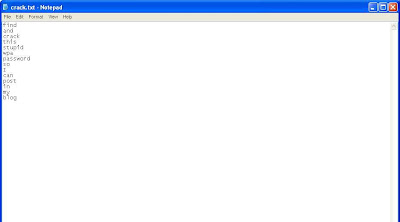
Okay okay, you got me. This was done in Windows XP. I forgot to take a screenshot of the list in BackTrack 3b, and was too lazy to go back and do it again. You'll just have to pretend its all black and fancy and cool looking like the BackTrack GUI is.
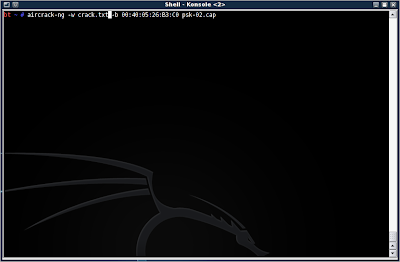
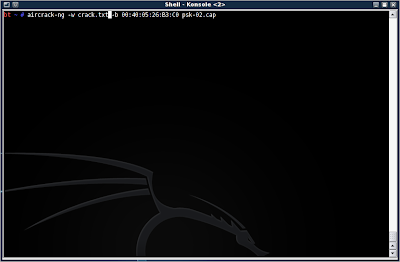
Alright, so you have your dictionary list ready to run with aircrack-ng. Type in aircrack-ng -w (dictionary.lst/txt) -b (AP MAC) (dumpfile.cap)
Mine has aircrack-ng -w crack.txt -b 00:40:05:26:B3:C0 psk-02.cap
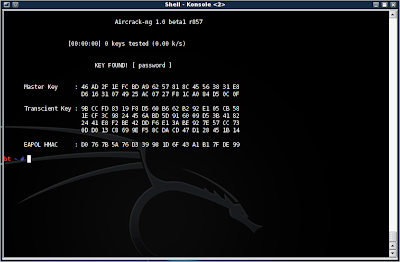
Now, if it finds the correct pass phrase in the dictionary list, you will be presented with the word:
Okay, so what did we learn here? Well, WPA-psk is more secure than WEP in that you must run a dictionary attack against it, and stronger passwords will require a rainbow table (don't worry, I may go into that in another blog). So it is theoretically more secure than WEP.
However, the pass phrase is only as secure as you make it. In this case, I set mine up to be very simple to facilitate this demonstration. However, using real words greatly diminishes the effectiveness of WPA, and it is highly suggested that you use special characters, upper case, lower case, and numbers in your passwords.
The second weakness in WPA-psk, is the reliance on the four-way handshake, in which the key is transmitted. It takes only a moment to run a deauth attack to force a handshake and grab the key.
Finally, WPA has the advantage of requiring a client to be connected before an attempt to crack can occur. Where WEP can be coaxed into transmitting packets, and therefore give the attacker IVs, WPA cracking needs that handshake with the pass phrase before any further progress can be made.
So WPA is far from perfect, but it can foil someone who is unprepared to run a dictionary attack, or with an unsuitable dictionary list.
TO BE CONTINUE
_____________________________________________________________________
Okay, so I'm not going to back track (forgive the pun) through the previous tutorial. If you aren't certain how to get to where I'm beginning this tutorial at, scroll down and read hacking WEP. It will fill you in on everything except putting your card into monitor mode and such.
So, first you will need to start up airodump-ng and capture packets from the AP. This time, however, do not add the --ivs, as you will want ALL the data in the packets. Look in the upper right corner of the window, just after the date and time. You will notice that the area is black and empty. This is where the four-way WPA handshake will show up when you have attained it. I will explain that in more detail later.
I will assume that you are now collecting packets in monitor mode. Packets by themselves are completely useless for cracking WPA. What we are interested in is the four-way handshake. To get this, we will use aireplay-ng to perform a deauth (de-authentication) attack, disconnecting the client from the AP, and forcing it to reconnect... also giving away the four-way handshake.
To do this, type in aireplay-ng -0 1 -a (AP MAC) -c (Client MAC) (your NIC)
Mine was aireplay-ng -0 1 -a 00:40:05:26:B3:C0 -c 00:16:CF:0B:0D:FD eth2
Now you should see a handshake appear in the window containing your running (you did leave it running, right?) airodump-ng program:
Now we need to get the key. Just as in the WEP cracking tutorial, I am going to make you do some of your own leg work. You will need to find a dictionary word list. You can also make your own, and add the pass phrase to the list. This screenshot shows an example of the list I made in a few seconds to show you the next steps:
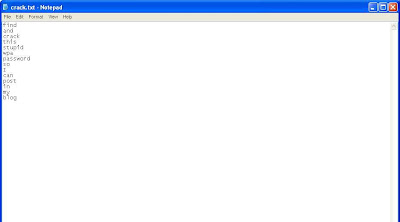
Okay okay, you got me. This was done in Windows XP. I forgot to take a screenshot of the list in BackTrack 3b, and was too lazy to go back and do it again. You'll just have to pretend its all black and fancy and cool looking like the BackTrack GUI is.
Alright, so you have your dictionary list ready to run with aircrack-ng. Type in aircrack-ng -w (dictionary.lst/txt) -b (AP MAC) (dumpfile.cap)
Mine has aircrack-ng -w crack.txt -b 00:40:05:26:B3:C0 psk-02.cap
Now, if it finds the correct pass phrase in the dictionary list, you will be presented with the word:
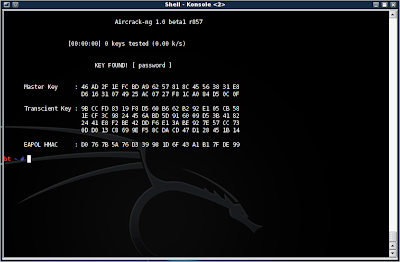
Okay, so what did we learn here? Well, WPA-psk is more secure than WEP in that you must run a dictionary attack against it, and stronger passwords will require a rainbow table (don't worry, I may go into that in another blog). So it is theoretically more secure than WEP.
However, the pass phrase is only as secure as you make it. In this case, I set mine up to be very simple to facilitate this demonstration. However, using real words greatly diminishes the effectiveness of WPA, and it is highly suggested that you use special characters, upper case, lower case, and numbers in your passwords.
The second weakness in WPA-psk, is the reliance on the four-way handshake, in which the key is transmitted. It takes only a moment to run a deauth attack to force a handshake and grab the key.
Finally, WPA has the advantage of requiring a client to be connected before an attempt to crack can occur. Where WEP can be coaxed into transmitting packets, and therefore give the attacker IVs, WPA cracking needs that handshake with the pass phrase before any further progress can be made.
So WPA is far from perfect, but it can foil someone who is unprepared to run a dictionary attack, or with an unsuitable dictionary list.
TO BE CONTINUE
Sunday, February 3, 2008
Creating a customized system restore disk
I was going to do another writeup on BackTrack, but I decided to do it on an often overlooked portion of network security: backup and restore.
It is inevitable that even your best defense will fail you, and the data center or workstations will need to be restored to their original state. Because attempting to do this with normal installation CDs would make a new career field, several methods have been devised for making streamlined install CDs and network installations.
I will not talk about restoring servers in this entry, but focus on workstations for smaller companies.
There are two main options for creating these restore CDs. The first is Bart, the second is nLite. After reviewing both of the programs (which are free and available for download), I decided to use nLite because of its greater simplicity. However, it will not allow me to 3rd party programs, only drivers, themes, service packs, and updates can be integrated. Bart also has the advantage of booting in live mode. However, nLite is much easier to setup and run, and requires no interaction from the user.
So, to start with, download all the drivers you want to install on your system. You will want the binaries if possible. If not, you will need to unpackage them. A program called Universal Extractor is good for doing this, but does not work with 100% of the drivers available.



Now you will need to download updates, either from Microsoft, or as a lump download from RyanMV. Put them into a folder as well.
After this, head to Microsoft and download service pack 2 for IT pros. This will allow you to install service pack 2 if your CD does not include it already. Also, you can download service pack 3 when it is ready.
After doing this, you will need to copy your windows XP cd to another folder. When it is completed, download and install nLite. Run it, and you will begin at this screen:

Its pretty straight forward. Next is this screen:

Here you must navigate to the file you copied your Windows XP cd to and load it.

This screen will allow you to import a previous session. Each session requires you to make a fresh copy of Windows XP. However, it will also allow you to modify previous ISO's without completely rebuilding them. Assuming you have no past sessions, simply click next.

Here is where you will choose what to streamline. For this exercise, I chose all of them:

And then selected service pack 2 for integration:

Be patient, it takes a little bit of time:

Once this is finished, navigate to the hot fixes and patches you wish to add to your installation:


Click next and you will be at the add drivers screen. Add the drivers you desire and click next.

After the drivers are finished integrating, you will need to select options you wish to keep. Don't worry, they won't remove any vital system options, they will only prevent you from removing a service that you wish to keep by accident. Think of this stage as a filter stage. You are asked what you wish to to do, and choices are narrowed down based on your more broad answers.

I have a webcam, needed DHCP functionality for networking, media center codecs, printers, windows activation (never turn this off unless you have a corporate edition disk) and I like to run automatic updates.

This is the important part. You can remove programs and drivers from being installed on your system. There is a plethora of features which the average user or office worker does not need. Everything from games, to messenger, down to different languages and ancient drivers.

As you can see, there is something in almost every category that can be removed. Keep in mind that most drivers do not use the generic windows pre-load drivers, but their own proprietary applications.

Now the fun part. You can fully automate the disk by entering the product key and selecting a fully automated unattended mode. I turned off system restore because I back up my files on a different drive, and like keeping the extra space (2% of 160 gigs is still a lot).

For safety concerns, I disabled the default administrator account, and gave my own account those permissions. Brute force attacks are run against Administrator and Admin accounts most frequently. You can also add additional users if you require.

This area allows you to configure your network. If you have a domain controller, enter the domain name, user name, and password, as well as the organization. The computer name will have to be changed after installation if this is the case, however.

Because I preloaded my nVidia video card drivers, I set the screen resolution and refresh rate to the optimal setting. WARNING!!! If you exceed your monitor or video card's maximum refresh rate or resolution, you can damage them! If you aren't sure what the threshold is, leave them at default and change it later.

I strongly advise turning automatic updates on, include minor updates, and elevate non-admins if there are non-admin accounts.

When you are finished reviewing and selecting your options, click next and double check the options screen. This will allow you to tweak a few additional options, especially in the boot process.

This screen allows you to tweak your startup an registry options. There are a few things that basic users can do, such as adding an administrative tools menu to the start menu (its a feature I really like from Server 2003).

After clicking next, nLite will begin to construct the files it will use to generate the ISO. Be patient, this takes some time. There may be errors in your updates. nLite can usually work around them and generate the files regardless.

Success!!! The total installation was reduced by 172.4 megabytes, even though I added 45.67 megabytes of additional drivers. This is a very slim installation, and will lead to a less bloated registry and windows folder.

Now just generate the ISO image. Once this image is created, you can put a writable disk into the CD drive, and double click the ISO. It will then create your installation CD. You can also use other ISO recording applications as well.
Remember to BE CAUTIOUS with these CDs. Unlike a Bart CD that installs from a server on the domain, these CDs can be swiped and used on any other computers. This is not good if you have a corporate license. I would advise that you make only a limited number of copies, secure the ISO file, and regulate the distribution of the CDs.
I will try to post a writeup using Bart CDs, though I cannot promise it will be using a domain for remote installation.
It is inevitable that even your best defense will fail you, and the data center or workstations will need to be restored to their original state. Because attempting to do this with normal installation CDs would make a new career field, several methods have been devised for making streamlined install CDs and network installations.
I will not talk about restoring servers in this entry, but focus on workstations for smaller companies.
There are two main options for creating these restore CDs. The first is Bart, the second is nLite. After reviewing both of the programs (which are free and available for download), I decided to use nLite because of its greater simplicity. However, it will not allow me to 3rd party programs, only drivers, themes, service packs, and updates can be integrated. Bart also has the advantage of booting in live mode. However, nLite is much easier to setup and run, and requires no interaction from the user.
So, to start with, download all the drivers you want to install on your system. You will want the binaries if possible. If not, you will need to unpackage them. A program called Universal Extractor is good for doing this, but does not work with 100% of the drivers available.



Now you will need to download updates, either from Microsoft, or as a lump download from RyanMV. Put them into a folder as well.
After this, head to Microsoft and download service pack 2 for IT pros. This will allow you to install service pack 2 if your CD does not include it already. Also, you can download service pack 3 when it is ready.
After doing this, you will need to copy your windows XP cd to another folder. When it is completed, download and install nLite. Run it, and you will begin at this screen:

Its pretty straight forward. Next is this screen:

Here you must navigate to the file you copied your Windows XP cd to and load it.

This screen will allow you to import a previous session. Each session requires you to make a fresh copy of Windows XP. However, it will also allow you to modify previous ISO's without completely rebuilding them. Assuming you have no past sessions, simply click next.

Here is where you will choose what to streamline. For this exercise, I chose all of them:

And then selected service pack 2 for integration:

Be patient, it takes a little bit of time:

Once this is finished, navigate to the hot fixes and patches you wish to add to your installation:


Click next and you will be at the add drivers screen. Add the drivers you desire and click next.

After the drivers are finished integrating, you will need to select options you wish to keep. Don't worry, they won't remove any vital system options, they will only prevent you from removing a service that you wish to keep by accident. Think of this stage as a filter stage. You are asked what you wish to to do, and choices are narrowed down based on your more broad answers.

I have a webcam, needed DHCP functionality for networking, media center codecs, printers, windows activation (never turn this off unless you have a corporate edition disk) and I like to run automatic updates.

This is the important part. You can remove programs and drivers from being installed on your system. There is a plethora of features which the average user or office worker does not need. Everything from games, to messenger, down to different languages and ancient drivers.

As you can see, there is something in almost every category that can be removed. Keep in mind that most drivers do not use the generic windows pre-load drivers, but their own proprietary applications.

Now the fun part. You can fully automate the disk by entering the product key and selecting a fully automated unattended mode. I turned off system restore because I back up my files on a different drive, and like keeping the extra space (2% of 160 gigs is still a lot).

For safety concerns, I disabled the default administrator account, and gave my own account those permissions. Brute force attacks are run against Administrator and Admin accounts most frequently. You can also add additional users if you require.

This area allows you to configure your network. If you have a domain controller, enter the domain name, user name, and password, as well as the organization. The computer name will have to be changed after installation if this is the case, however.

Because I preloaded my nVidia video card drivers, I set the screen resolution and refresh rate to the optimal setting. WARNING!!! If you exceed your monitor or video card's maximum refresh rate or resolution, you can damage them! If you aren't sure what the threshold is, leave them at default and change it later.

I strongly advise turning automatic updates on, include minor updates, and elevate non-admins if there are non-admin accounts.

When you are finished reviewing and selecting your options, click next and double check the options screen. This will allow you to tweak a few additional options, especially in the boot process.

This screen allows you to tweak your startup an registry options. There are a few things that basic users can do, such as adding an administrative tools menu to the start menu (its a feature I really like from Server 2003).

After clicking next, nLite will begin to construct the files it will use to generate the ISO. Be patient, this takes some time. There may be errors in your updates. nLite can usually work around them and generate the files regardless.

Success!!! The total installation was reduced by 172.4 megabytes, even though I added 45.67 megabytes of additional drivers. This is a very slim installation, and will lead to a less bloated registry and windows folder.

Now just generate the ISO image. Once this image is created, you can put a writable disk into the CD drive, and double click the ISO. It will then create your installation CD. You can also use other ISO recording applications as well.
Remember to BE CAUTIOUS with these CDs. Unlike a Bart CD that installs from a server on the domain, these CDs can be swiped and used on any other computers. This is not good if you have a corporate license. I would advise that you make only a limited number of copies, secure the ISO file, and regulate the distribution of the CDs.
I will try to post a writeup using Bart CDs, though I cannot promise it will be using a domain for remote installation.
Friday, February 1, 2008
Ethical Implications of Hacking
This is not an entry that I am making from what I have learned from reading a book or browsing websites, but from interaction as a network infrastructure intern, computer technician hobbyist, and help desk employee. It is a bit of wisdom and musing that has been mixed together and coughed up into a paper. I think I would have rather done more work with BackTrack 3b, but I've run out of time this week. So do not look for any sources past my own personal experience on this matter.
As I learn and discover more in the ways of hacking, the greater I find the urge to try what I have learned on systems other than my own. Then I remind myself that it is no less than looking through someone's window. Is it morally right to stand outside a stranger's house and watch them through a window? Of course not, so why would it be any different to do it through a computer?
I believe the anonymity of hacking is what emboldens people, makes them feel empowered and just in their ability to gain access to personal documents, even if they do no harm. Yet this invasive behavior could only breed distrust and anger on any other level.
But the subjects of ethics is not relegated to adults. Is it ethical to teach someone young, perhaps in junior high, to hack computer systems? It is certainly possible for younger generations to learn at an early age, even as young as grade school. However, knowing and understanding are two very different principles. While script kiddies are dangerous, a full, bona fide hacker of that age still has no understanding of the harm they can cause, yet has more power to infiltrate private systems.
Without a firm grasp of ethics or understanding, the juvenile will then cause damage to the system, the result of which could cost millions. At the same time, however, an early exposure to such knowledge could give the child a head start on a lucrative career path. And the earlier they begin, the more potential they will have in the field of information security.
Perhaps, then, the ethical thing would not be to expose or deny, but to regulate access and activities involving this knowledge. Ultimately, the outcome of a child's life is dependent on their parents or guardians.
There is also a code of ethics for the workplace. Even for those not in a network security position, or even in the IT department. Having similar skills and knowledge does not give them a right to employ it. It may be that the services are required from time to time, or not at all. But services are limited to what an administrator would ask of the employee.
Using such skills because another employee needs access to restricted files, forgot their password, or wants to delete an email containing questionable material that they accidentally sent to the boss, is unethical. All networks are privately owned, and even administrators must practice self restraint.
And why should such care be taken if nobody will know? Indeed they may not know of that offense. However, all members of the Information Technology department make other employees nervous. We are often viewed as key holders, overseers, and judges. I have seen for myself the widespread belief that we have access to all information, records on all the employees, and know their computing habits by heart.
To become what people believe will enforce the notion that we are a body to be resisted, a department that spends the day finding reasons to fire or reprimand, and reduce the freedoms of other employees. To prevent this, it is the duty of all, in IT or not, who possess such skills to hack, to keep to the code of ethics and refrain from activities that would tarnish or reduce employee's faith in IT.
And those who live under the strongest code of ethics, the penetration testers and security administrators, must hold even closer to the code of ethics. Security administrators cannot break the code of ethics for the top level of management within a company. Likewise, penetration testers must attempt to access information that could be crippling to individuals or the company to ensure its safety. They are entrusted with many company secrets, and to release any vulnerabilities to the company instead of exploiting them for personal gain.
As I learn and discover more in the ways of hacking, the greater I find the urge to try what I have learned on systems other than my own. Then I remind myself that it is no less than looking through someone's window. Is it morally right to stand outside a stranger's house and watch them through a window? Of course not, so why would it be any different to do it through a computer?
I believe the anonymity of hacking is what emboldens people, makes them feel empowered and just in their ability to gain access to personal documents, even if they do no harm. Yet this invasive behavior could only breed distrust and anger on any other level.
But the subjects of ethics is not relegated to adults. Is it ethical to teach someone young, perhaps in junior high, to hack computer systems? It is certainly possible for younger generations to learn at an early age, even as young as grade school. However, knowing and understanding are two very different principles. While script kiddies are dangerous, a full, bona fide hacker of that age still has no understanding of the harm they can cause, yet has more power to infiltrate private systems.
Without a firm grasp of ethics or understanding, the juvenile will then cause damage to the system, the result of which could cost millions. At the same time, however, an early exposure to such knowledge could give the child a head start on a lucrative career path. And the earlier they begin, the more potential they will have in the field of information security.
Perhaps, then, the ethical thing would not be to expose or deny, but to regulate access and activities involving this knowledge. Ultimately, the outcome of a child's life is dependent on their parents or guardians.
There is also a code of ethics for the workplace. Even for those not in a network security position, or even in the IT department. Having similar skills and knowledge does not give them a right to employ it. It may be that the services are required from time to time, or not at all. But services are limited to what an administrator would ask of the employee.
Using such skills because another employee needs access to restricted files, forgot their password, or wants to delete an email containing questionable material that they accidentally sent to the boss, is unethical. All networks are privately owned, and even administrators must practice self restraint.
And why should such care be taken if nobody will know? Indeed they may not know of that offense. However, all members of the Information Technology department make other employees nervous. We are often viewed as key holders, overseers, and judges. I have seen for myself the widespread belief that we have access to all information, records on all the employees, and know their computing habits by heart.
To become what people believe will enforce the notion that we are a body to be resisted, a department that spends the day finding reasons to fire or reprimand, and reduce the freedoms of other employees. To prevent this, it is the duty of all, in IT or not, who possess such skills to hack, to keep to the code of ethics and refrain from activities that would tarnish or reduce employee's faith in IT.
And those who live under the strongest code of ethics, the penetration testers and security administrators, must hold even closer to the code of ethics. Security administrators cannot break the code of ethics for the top level of management within a company. Likewise, penetration testers must attempt to access information that could be crippling to individuals or the company to ensure its safety. They are entrusted with many company secrets, and to release any vulnerabilities to the company instead of exploiting them for personal gain.
Subscribe to:
Posts (Atom)